Applied Sciences | Free Full-Text | Cybersecurity and Network Forensics: Analysis of Malicious Traffic towards a Honeynet with Deep Packet Inspection
alienvault-ossim/suricata-rules-default-open/rules/1.3.1/emerging.rules/emerging-scan.rules at master · jpalanco/alienvault-ossim · GitHub
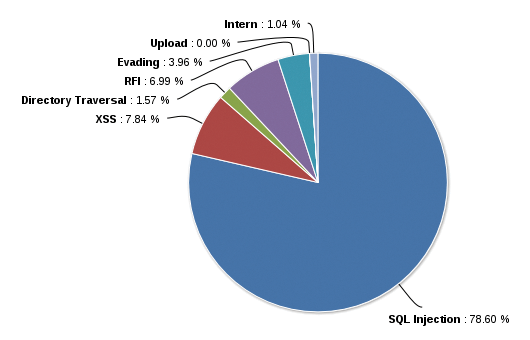
Applied Sciences | Free Full-Text | Cybersecurity and Network Forensics: Analysis of Malicious Traffic towards a Honeynet with Deep Packet Inspection

September 2020's Most Wanted Malware: New Info-stealing Valak Variant Enters Top 10 Malware List For First Time - Check Point Blog

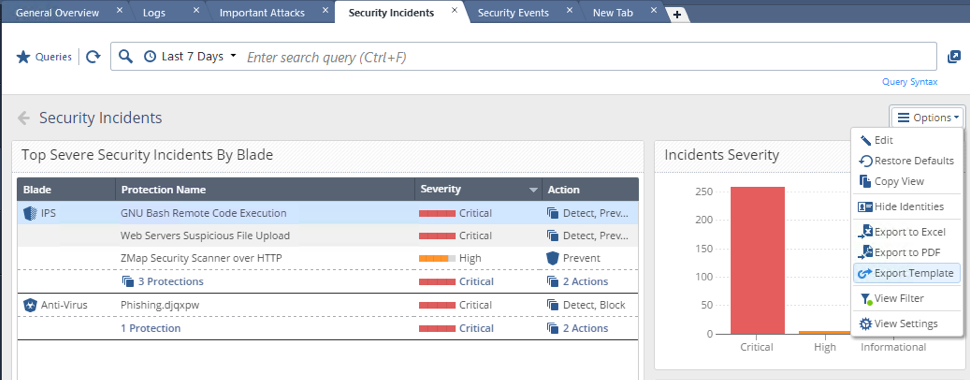
Cloud SIEM | Logz.io | Easily secure distributed cloud workloads with simplified, DevOps-native threat detection and Kibana analytics! See Logz.io Cloud SIEM in action! #DevSecOps | By Logz.io | Facebook
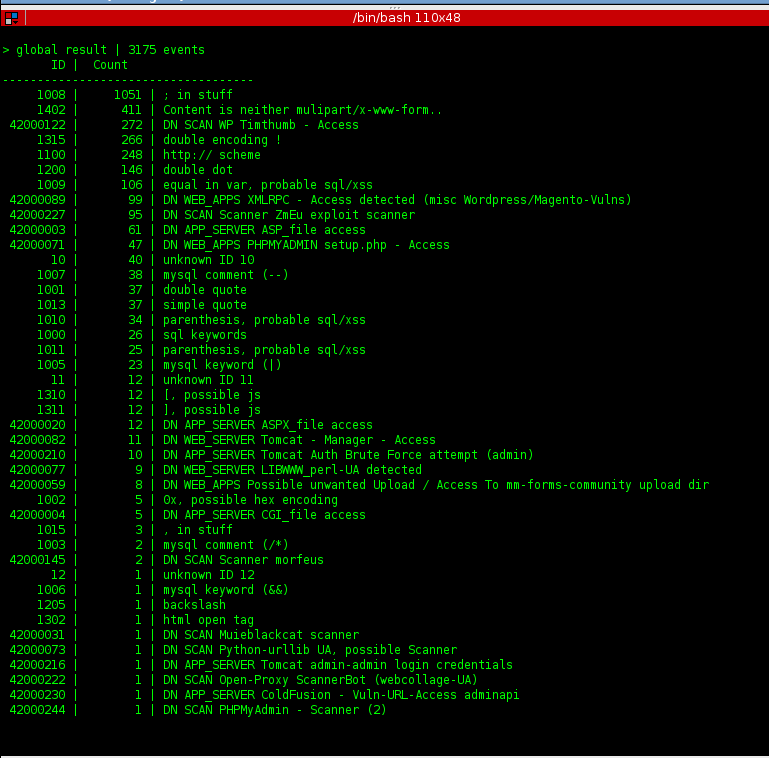
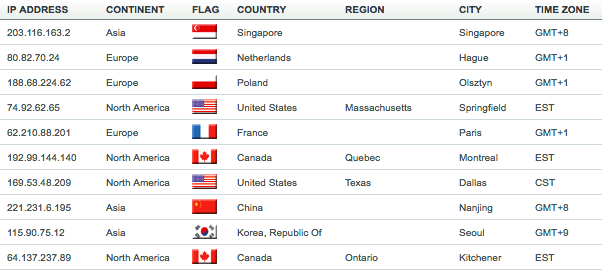
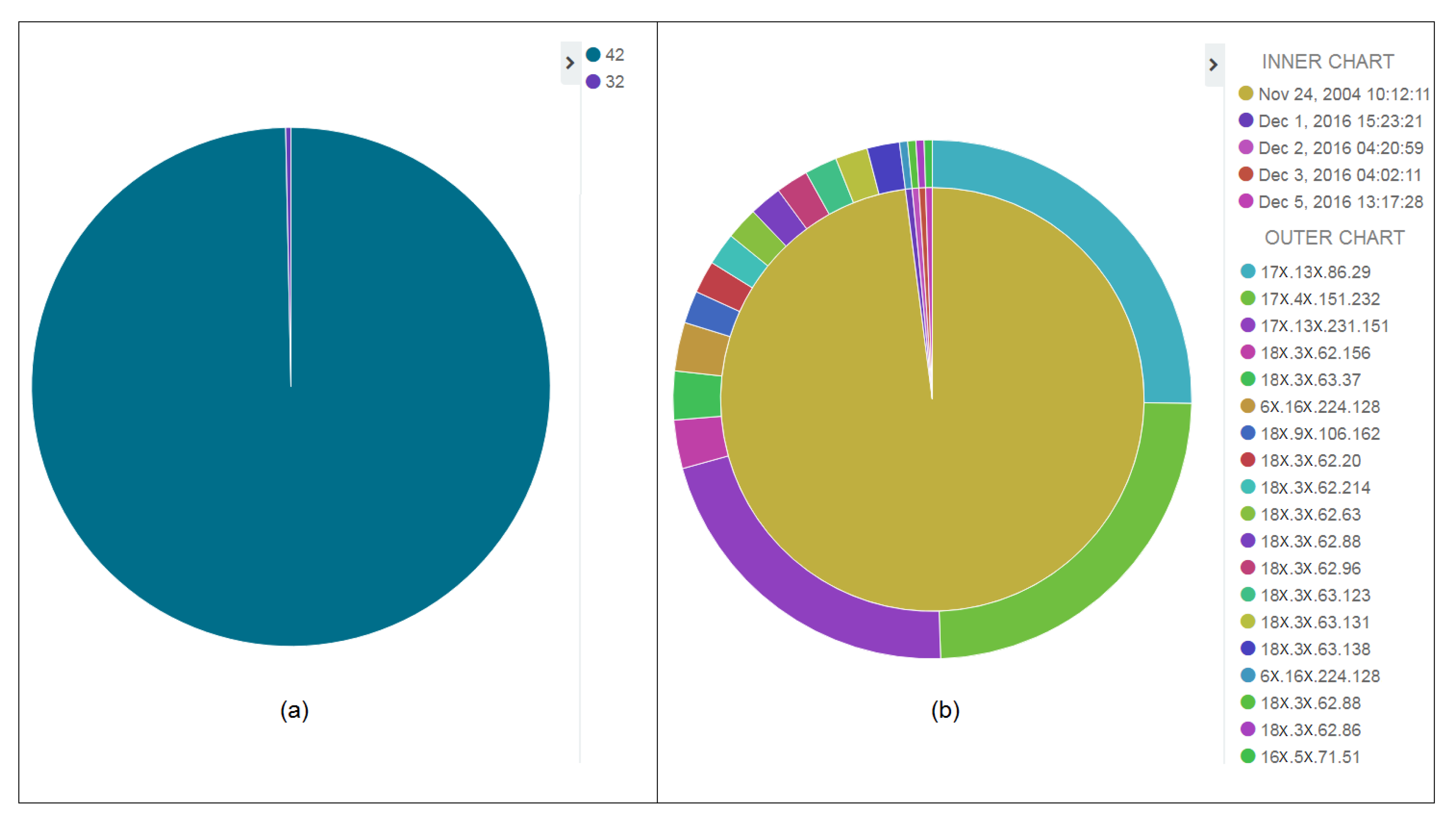
![PDF] Cybersecurity and Network Forensics: Analysis of Malicious Traffic towards a Honeynet with Deep Packet Inspection | Semantic Scholar PDF] Cybersecurity and Network Forensics: Analysis of Malicious Traffic towards a Honeynet with Deep Packet Inspection | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/860a4998e2a25d732db28f84f6d503bfc6e1f00c/22-Table9-1.png)